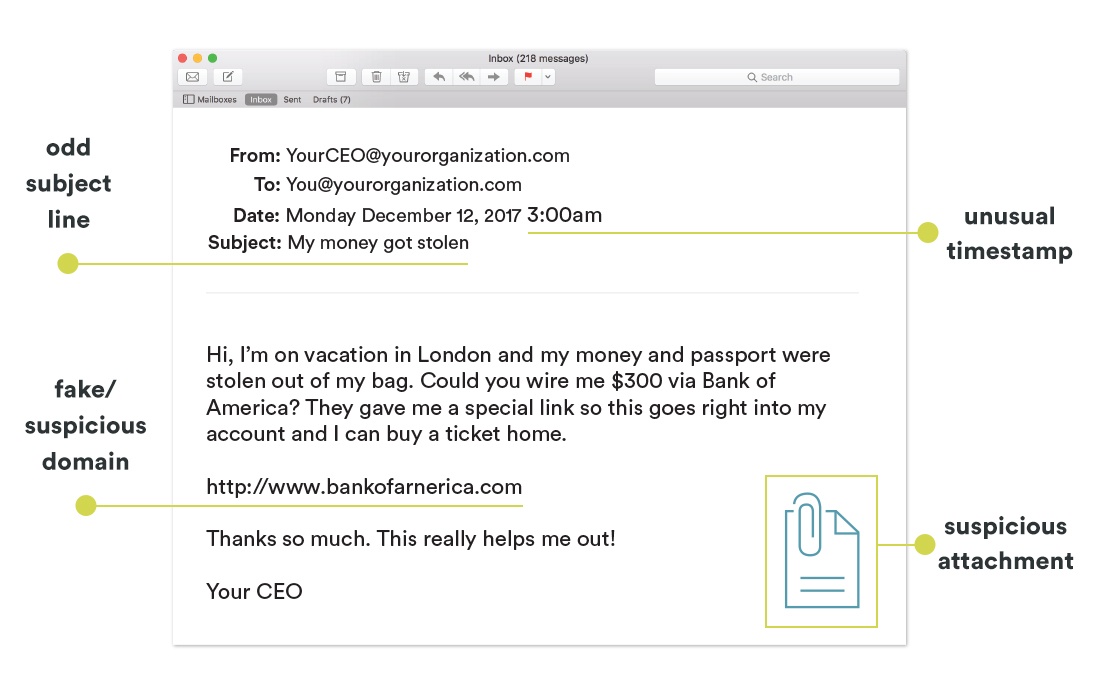
Over the past few months, we've seen that plenty of phishing emails are on the rise that are impacting users personally and professionally. We've covered common tactics from phishing attackers and how the coronavirus pandemic has given even more opportunities for scammers to take advantage of vulnerable victims. Let's break down the anatomy of a phishing email and identify some easy ways that you can pick phishing attempts out from the sea of messages in your inbox.
Phishing Questionnaire Checklist
When you believe that a message may be an attempt at phishing, taking the time to ask these questions can help you stay on the lookout for telltale signs that someone is trying to gain access to your sensitive data.
Who is the email from?
- Do you recognize the senders email address as someone you usually communicate with, have a business relationship with, or has been vouched for by someone you trust?
- Is the email from a suspicious domain? (be on the lookout for unusual characters, spelling or punctuation, i.e. @micorsoft-support.com)
Who is the email to?
-
Were you cc’d on an email to multiple people that you don’t personally know? This could be random group of people at your organization whose last names start with the same letter, or even a whole list of unrelated addresses.
When was the email sent?
-
Was this an email you would normally receive during business hours, but it came at an unusual time such as 3am or during a weekend or holiday?
What’s in the subject line?
-
Does the subject line match the message content or seem relevant?
-
Did you receive a reply to something you never sent or requested?
Does the content seem odd?
-
Is the sender asking you to click a link or open an attachment in order to avoid a negative consequence, gain something of value, or for any reason that seems odd or illogical?
-
Does the email content seem unusual or out of character for the person you received it from? Was it unexpected?
-
Is the email asking you to look at compromising or embarrassing pictures?
-
Are there bad spelling or grammar errors in the message?
Are there any suspicious attachments or hyperlinks?
-
Did the sender include an attachment that you weren’t expecting or that doesn’t make sense in the context of the email?
-
Does the attachment have a possibly dangerous file type? (The only file type that is always safe to click on is a .txt file)
-
When you hover over the hyperlink, does it show a link-to address that is different than what is displayed? (This is a BIG red flag! ⛳️)
-
Does the hyperlink have a misspelling of a known website? For instance, www.bankofarnerica.com - the “m” is really two characters - “r” and “n”.
While these questions may not always address every concern, they are an important security step that can help make the right call when a suspicious email comes your way! Phishing attackers are always finding new ways to shift their strategies and take advantage of the latest loopholes and strategies that can help them trick users into sharing their personal information.
SeedSpark stays tuned into the world of cybersecurity, providing multiple levels of security that help ourselves and our clients stay safe when working and communicating online in the modern marketplace.